 Free stand-alone utility used to detect and remove specific viruses
Free stand-alone utility used to detect and remove specific viruses
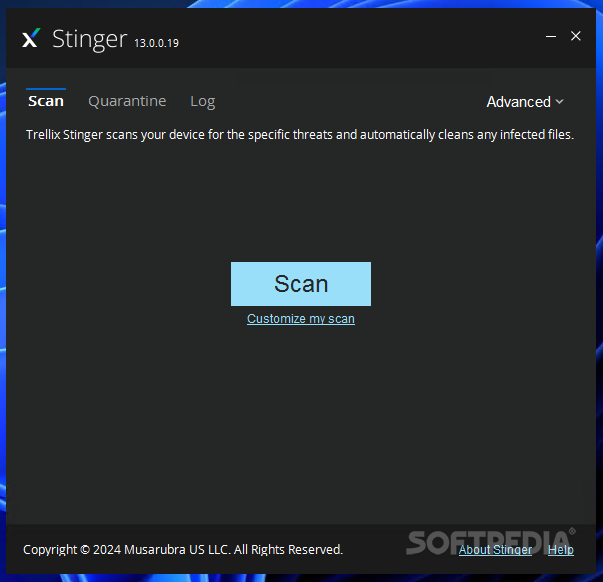
Stinger is a stand-alone utility used to detect and remove specific viruses.
McAfee AVERT Stinger is not a substitute for the full anti-virus protection, but rather a tool that assists administrators and users when dealing with an infected system.
Stinger utilizes next generation scan engine technology, including process scanning, digitally signed DAT files, and scan performance optimizations.
This version of Stinger includes detection for all known variants :
■ BackDoor-ALI
■ BackDoor-AQJ
■ BackDoor-AQJ.b
■ BackDoor-CEB
■ BackDoor-CEB!bat
■ BackDoor-CEB!hosts
■ BackDoor-CEB.b
■ BackDoor-CEB.c
■ BackDoor-CEB.d
■ BackDoor-CEB.dll
■ BackDoor-CEB.dr
■ BackDoor-CEB.e
■ BackDoor-CEB.f
■ BackDoor-CEB.sys
■ BackDoor-CFB
■ BackDoor-JZ
■ BackDoor-JZ.dam
■ BackDoor-JZ.dr
■ BackDoor-JZ.gen
■ BackDoor-JZ.gen.b
■ Bat/Mumu.worm
■ Downloader-DN.a
■ Downloader-DN.b
■ Exploit-DcomRpc
■ Exploit-DcomRpc.b
■ Exploit-DcomRpc.dll
■ Exploit-Lsass
■ Exploit-Lsass.dll
■ Exploit-MS04-011
■ Exploit-MS04-011.gen
■ HideWindow
■ HideWindow.dll
■ IPCScan
■ IRC/Flood.ap
■ IRC/Flood.ap.bat
■ IRC/Flood.ap.dr
■ IRC/Flood.bi
■ IRC/Flood.bi.dr
■ IRC/Flood.cd
■ NTServiceLoader
■ ProcKill
■ PWS-Narod
■ PWS-Narod.dll
■ PWS-Narod.gen
■ PWS-Sincom
■ PWS-Sincom.dll
■ PWS-Sincom.dr
■ W32/Anig.worm
■ W32/Anig.worm.dll
■ W32/Bagle
■ W32/Bagle!eml.gen
■ W32/Bagle!pwdzip
■ W32/Bagle.ad!src
■ W32/Bagle.dldr
■ W32/Bagle.dll.dr
■ W32/Bagle.eml
■ W32/Bagle.fb!pwdzip
■ W32/Bagle.fc!pwdzip
■ W32/Bagle.fd!pwdzip
■ W32/Bagle.fe!pwdzip
■ W32/Bagle.fm.dldr
■ W32/Bagle.gen
■ W32/Bagle@MM!cpl
■ W32/Blaster.worm
■ W32/Blaster.worm.k
■ W32/Bropia.worm
■ W32/Bugbear
■ W32/Bugbear.a.dam
■ W32/Bugbear.b!data
■ W32/Bugbear.b.dam
■ W32/Bugbear.gen@MM
■ W32/Bugbear.h@MM
■ W32/Bugbear@MM
■ W32/Deborm.worm.ah
■ W32/Deborm.worm.gen
■ W32/Doomjuice.worm
■ W32/Dumaru
■ W32/Dumaru.ad@MM
■ W32/Dumaru.al.dll
■ W32/Dumaru.dll
■ W32/Dumaru.eml
■ W32/Dumaru.gen
■ W32/Dumaru.gen@MM
■ W32/Dumaru.w.gen
■ W32/Elkern.cav
■ W32/Elkern.cav.c
■ W32/Elkern.cav.c.dam
■ W32/Fizzer
■ W32/Fizzer.dll
■ W32/FunLove
■ W32/FunLove.apd
■ W32/Gaobot.worm
■ W32/Harwig.worm
■ W32/IRCbot
■ W32/IRCbot.worm
■ W32/IRCbot.worm.dll
■ W32/Klez
■ W32/Klez.dam
■ W32/Klez.eml
■ W32/Klez.gen.b@MM
■ W32/Klez.rar
■ W32/Korgo.worm
■ W32/Lirva
■ W32/Lirva.c.htm
■ W32/Lirva.eml
■ W32/Lirva.gen@MM
■ W32/Lirva.htm
■ W32/Lirva.txt
■ W32/Lovgate
■ W32/Mimail
■ W32/Mimail.c@MM
■ W32/Mimail.c@MM
■ W32/Mimail.i!data
■ W32/Mimail.q@MM
■ W32/MoFei.worm
■ W32/MoFei.worm.dr
■ W32/Mumu.b.worm
■ W32/Mydoom
■ W32/Mydoom!bat
■ W32/Mydoom!ftp
■ W32/Mydoom.b!hosts
■ W32/Mydoom.dam
■ W32/Mydoom.t.dll
■ W32/Mytob
■ W32/Mytob.gen@MM
■ W32/Mytob.worm
■ W32/MyWife
■ W32/MyWife.dll
■ W32/MyWife@MM
■ W32/Nachi!tftpd
■ W32/Nachi.worm
■ W32/Netsky
■ W32/Netsky.af@MM
■ W32/Nimda
■ W32/Nimda.dam
■ W32/Nimda.eml
■ W32/Nimda.gen@MM
■ W32/Nimda.htm
■ W32/Pate
■ W32/Pate!dam
■ W32/Pate.dam
■ W32/Pate.dr
■ W32/Polip
■ W32/Polip!mem
■ W32/Polybot
■ W32/Polybot.bat
■ W32/Sasser.worm
■ W32/Sasser.worm!ftp
■ W32/Sdbot
■ W32/Sdbot!irc
■ W32/Sdbot.bat
■ W32/Sdbot.cli
■ W32/Sdbot.dll
■ W32/Sdbot.dr
■ W32/Sdbot.worm
■ W32/Sdbot.worm!ftp
■ W32/Sdbot.worm.bat.b
■ W32/Sdbot.worm.dr
■ W32/Sdbot.worm.gen
■ W32/Sdbot.worm.gen.a
■ W32/Sdbot.worm.gen.b
■ W32/Sdbot.worm.gen.c
■ W32/Sdbot.worm.gen.d
■ W32/Sdbot.worm.gen.e
■ W32/Sdbot.worm.gen.q
■ W32/Sober
■ W32/Sober!data
■ W32/Sober.dam
■ W32/Sober.eml
■ W32/Sober.f.dam
■ W32/Sober.g.dam
■ W32/Sober.q!spam
■ W32/Sober.r.dr
■ W32/Sober.r@MM
■ W32/Sobig
■ W32/Sobig.dam
■ W32/Sobig.eml
■ W32/Sobig.f.dam
■ W32/Sobig.gen@MM
■ W32/Spybot.worm
■ W32/SQLSlammer.worm
■ W32/Swen
■ W32/Swen@MM
■ W32/Yaha.eml
■ W32/Yaha.gen@MM
■ W32/Yaha.y@MM
■ W32/Yaha@MM
■ W32/Zafi
■ W32/Zafi.b.dam
■ W32/Zindos.worm
■ W32/Zotob.worm
■ W32/Zotob.worm!hosts
Note: Windows ME and XP utilize a restore utility that backs up selected files automatically to the C:_Restore folder.
The filename has been changed from "stinger.exe" to "s-t-i-n-g-e-r.exe" to circumvent anti-stinger tactics used by Sober.p.
This means that an infected file could be stored there as a backup file, and VirusScan will be unable to delete these files. You must disable the System Restore Utility to remove the infected files from the C:_Restore folder.
Credits To - Softpedia
McAfee AVERT Stinger is not a substitute for the full anti-virus protection, but rather a tool that assists administrators and users when dealing with an infected system.
Stinger utilizes next generation scan engine technology, including process scanning, digitally signed DAT files, and scan performance optimizations.
This version of Stinger includes detection for all known variants :
■ BackDoor-ALI
■ BackDoor-AQJ
■ BackDoor-AQJ.b
■ BackDoor-CEB
■ BackDoor-CEB!bat
■ BackDoor-CEB!hosts
■ BackDoor-CEB.b
■ BackDoor-CEB.c
■ BackDoor-CEB.d
■ BackDoor-CEB.dll
■ BackDoor-CEB.dr
■ BackDoor-CEB.e
■ BackDoor-CEB.f
■ BackDoor-CEB.sys
■ BackDoor-CFB
■ BackDoor-JZ
■ BackDoor-JZ.dam
■ BackDoor-JZ.dr
■ BackDoor-JZ.gen
■ BackDoor-JZ.gen.b
■ Bat/Mumu.worm
■ Downloader-DN.a
■ Downloader-DN.b
■ Exploit-DcomRpc
■ Exploit-DcomRpc.b
■ Exploit-DcomRpc.dll
■ Exploit-Lsass
■ Exploit-Lsass.dll
■ Exploit-MS04-011
■ Exploit-MS04-011.gen
■ HideWindow
■ HideWindow.dll
■ IPCScan
■ IRC/Flood.ap
■ IRC/Flood.ap.bat
■ IRC/Flood.ap.dr
■ IRC/Flood.bi
■ IRC/Flood.bi.dr
■ IRC/Flood.cd
■ NTServiceLoader
■ ProcKill
■ PWS-Narod
■ PWS-Narod.dll
■ PWS-Narod.gen
■ PWS-Sincom
■ PWS-Sincom.dll
■ PWS-Sincom.dr
■ W32/Anig.worm
■ W32/Anig.worm.dll
■ W32/Bagle
■ W32/Bagle!eml.gen
■ W32/Bagle!pwdzip
■ W32/Bagle.ad!src
■ W32/Bagle.dldr
■ W32/Bagle.dll.dr
■ W32/Bagle.eml
■ W32/Bagle.fb!pwdzip
■ W32/Bagle.fc!pwdzip
■ W32/Bagle.fd!pwdzip
■ W32/Bagle.fe!pwdzip
■ W32/Bagle.fm.dldr
■ W32/Bagle.gen
■ W32/Bagle@MM!cpl
■ W32/Blaster.worm
■ W32/Blaster.worm.k
■ W32/Bropia.worm
■ W32/Bugbear
■ W32/Bugbear.a.dam
■ W32/Bugbear.b!data
■ W32/Bugbear.b.dam
■ W32/Bugbear.gen@MM
■ W32/Bugbear.h@MM
■ W32/Bugbear@MM
■ W32/Deborm.worm.ah
■ W32/Deborm.worm.gen
■ W32/Doomjuice.worm
■ W32/Dumaru
■ W32/Dumaru.ad@MM
■ W32/Dumaru.al.dll
■ W32/Dumaru.dll
■ W32/Dumaru.eml
■ W32/Dumaru.gen
■ W32/Dumaru.gen@MM
■ W32/Dumaru.w.gen
■ W32/Elkern.cav
■ W32/Elkern.cav.c
■ W32/Elkern.cav.c.dam
■ W32/Fizzer
■ W32/Fizzer.dll
■ W32/FunLove
■ W32/FunLove.apd
■ W32/Gaobot.worm
■ W32/Harwig.worm
■ W32/IRCbot
■ W32/IRCbot.worm
■ W32/IRCbot.worm.dll
■ W32/Klez
■ W32/Klez.dam
■ W32/Klez.eml
■ W32/Klez.gen.b@MM
■ W32/Klez.rar
■ W32/Korgo.worm
■ W32/Lirva
■ W32/Lirva.c.htm
■ W32/Lirva.eml
■ W32/Lirva.gen@MM
■ W32/Lirva.htm
■ W32/Lirva.txt
■ W32/Lovgate
■ W32/Mimail
■ W32/Mimail.c@MM
■ W32/Mimail.c@MM
■ W32/Mimail.i!data
■ W32/Mimail.q@MM
■ W32/MoFei.worm
■ W32/MoFei.worm.dr
■ W32/Mumu.b.worm
■ W32/Mydoom
■ W32/Mydoom!bat
■ W32/Mydoom!ftp
■ W32/Mydoom.b!hosts
■ W32/Mydoom.dam
■ W32/Mydoom.t.dll
■ W32/Mytob
■ W32/Mytob.gen@MM
■ W32/Mytob.worm
■ W32/MyWife
■ W32/MyWife.dll
■ W32/MyWife@MM
■ W32/Nachi!tftpd
■ W32/Nachi.worm
■ W32/Netsky
■ W32/Netsky.af@MM
■ W32/Nimda
■ W32/Nimda.dam
■ W32/Nimda.eml
■ W32/Nimda.gen@MM
■ W32/Nimda.htm
■ W32/Pate
■ W32/Pate!dam
■ W32/Pate.dam
■ W32/Pate.dr
■ W32/Polip
■ W32/Polip!mem
■ W32/Polybot
■ W32/Polybot.bat
■ W32/Sasser.worm
■ W32/Sasser.worm!ftp
■ W32/Sdbot
■ W32/Sdbot!irc
■ W32/Sdbot.bat
■ W32/Sdbot.cli
■ W32/Sdbot.dll
■ W32/Sdbot.dr
■ W32/Sdbot.worm
■ W32/Sdbot.worm!ftp
■ W32/Sdbot.worm.bat.b
■ W32/Sdbot.worm.dr
■ W32/Sdbot.worm.gen
■ W32/Sdbot.worm.gen.a
■ W32/Sdbot.worm.gen.b
■ W32/Sdbot.worm.gen.c
■ W32/Sdbot.worm.gen.d
■ W32/Sdbot.worm.gen.e
■ W32/Sdbot.worm.gen.q
■ W32/Sober
■ W32/Sober!data
■ W32/Sober.dam
■ W32/Sober.eml
■ W32/Sober.f.dam
■ W32/Sober.g.dam
■ W32/Sober.q!spam
■ W32/Sober.r.dr
■ W32/Sober.r@MM
■ W32/Sobig
■ W32/Sobig.dam
■ W32/Sobig.eml
■ W32/Sobig.f.dam
■ W32/Sobig.gen@MM
■ W32/Spybot.worm
■ W32/SQLSlammer.worm
■ W32/Swen
■ W32/Swen@MM
■ W32/Yaha.eml
■ W32/Yaha.gen@MM
■ W32/Yaha.y@MM
■ W32/Yaha@MM
■ W32/Zafi
■ W32/Zafi.b.dam
■ W32/Zindos.worm
■ W32/Zotob.worm
■ W32/Zotob.worm!hosts
Note: Windows ME and XP utilize a restore utility that backs up selected files automatically to the C:_Restore folder.
The filename has been changed from "stinger.exe" to "s-t-i-n-g-e-r.exe" to circumvent anti-stinger tactics used by Sober.p.
This means that an infected file could be stored there as a backup file, and VirusScan will be unable to delete these files. You must disable the System Restore Utility to remove the infected files from the C:_Restore folder.
Credits To - Softpedia
Categories:
Antivirus
